
CAC authentication has gotten faster with better hardware and smarter configurations, but most DoD users are still working with setups that haven’t been optimized since the card reader was issued. As someone who has spent more time waiting for readers to detect cards and browsers to present certificates than I care to calculate, I learned what actually reduces that friction. Today, I will share it all with you.
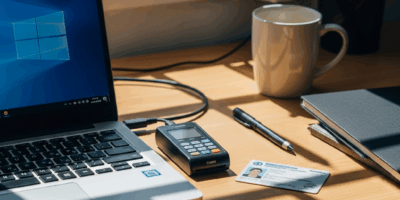
Smart Card Readers That Actually Perform
The physical reader is where efficiency often dies first. Cheap USB readers have longer recognition delay, occasional detection failures, and poor build quality. Readers worth using:
The HID OMNIKEY 3021 is widely deployed on government systems for good reason — reliable detection and solid middleware compatibility. The SCM SCR3310v2 has an updated design with good driver support and a faster chip contact. Both are a meaningful upgrade over bargain readers.
For laptops, an integrated smart card reader eliminates the external dongle entirely. Dell, HP, and Lenovo business-class laptops commonly include them. If you’re buying equipment for CAC-heavy work, this is the spec to look for — it’s the fastest and most reliable setup available.
USB-C and Modern Port Compatibility
The shift to USB-C-only laptops created real problems for CAC users. The fix is a USB-C hub with an integrated smart card reader — Targus makes a version worth considering. Not all USB hubs handle the timing requirements of smart card communication correctly, so verify your hub has been tested for smart card use before committing to it.
ActivClient Settings Worth Configuring
If your organization runs ActivClient 7.x, a few features reduce daily friction significantly. Single Sign-On integration, when configured properly, caches the PIN in memory after a single entry per session rather than requiring PIN entry for every application. Certificate Selector Memory remembers which certificate you’ve selected for which site. Auto-Remove Detection locks the workstation immediately when the card is removed — both a security feature and a convenience feature that eliminates the need for manual locking.
Windows Hello for Business
Windows Hello for Business provides PIN or biometric authentication to Windows alongside (not replacing) the CAC. On properly configured machines, you can unlock the workstation with Windows Hello while the CAC remains required for DoD system authentication. The combination reduces how often you physically need the card while maintaining PKI authentication where it’s required — particularly useful when your workstation locks and unlocks frequently throughout the day.
Browser Extensions for DoD Sites
A DoD Root Certificates extension for Chrome can maintain current DoD root certificates in the browser without requiring the full InstallRoot installation process — useful for personal devices used for DoD access. Some third-party extensions also provide middleware-like functionality for browser-based CAC authentication, though policy acceptance varies by command. Verify acceptability before installing anything on a government machine.
Workflow Habits That Cut Time
Hardware and software aside, habits make a difference. Leave the card inserted during active work sessions rather than inserting and removing for each transaction if your workstation policy allows it. A retractable badge reel that clips to your reader keeps the card physically accessible without hunting through a pocket every time. Configure screen lock intervals at the shortest interval that satisfies policy without creating constant re-authentication cycles — this is worth a conversation with your security officer if the current setting seems unnecessarily short.
Most CAC problems are human factors problems. Knowing your specific setup’s quirks, keeping ActivClient updated, and having a consistent authentication routine dramatically reduces the daily friction without any additional hardware investment.


Leave a Reply